Congress overwhelmingly voted for the Patriot Act nearly 16 years ago, and our civil liberties have never been the same since. As if this singular bill, passed by George W. Bush, wasn’t invasive enough, allowing big banks to demand our Internet data, and more — the Cybersecurity Information Sharing Act (CISA) makes cyber-spying by the shadow government and the financial entities controlling it, a forgone conclusion.
As with most shadow government legislation, the Cybersecurity Information Sharing Act is packed with hidden surveillance allowances. CISA was quietly passed to allow government to demand that private companies hand over personal information to them at will. It also allows companies to mine data, under the auspices of government-created urgency.
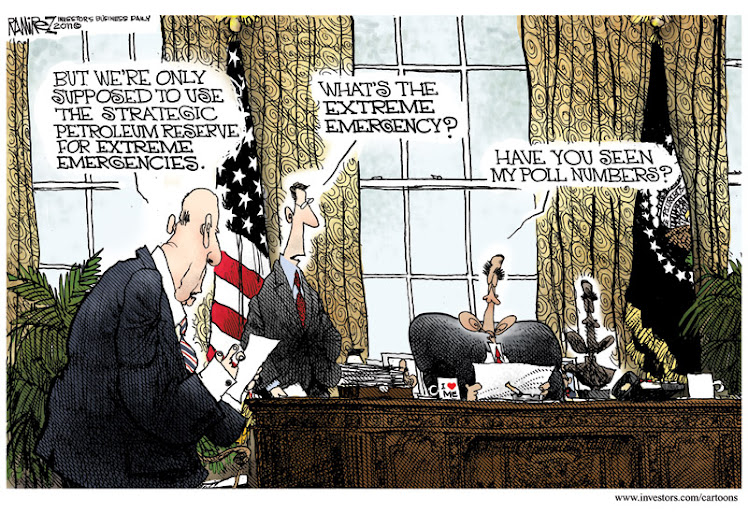
The mere fact that this Act passed in late 2015 is monumental, since it has been before Congress in different forms for over a decade. The election seems to have offered the perfect cover, as Americans and activists were too busy arguing over Trump vs. Hillary.
Scott Talbott, senior vice president of government relations at the Electronic Transactions Association believes the value of sharing our personal data as a means to be alerted of ‘cyber threats’ outweighs any hazard to our civil liberties. Talbott states,
“The value is that everyone can be alerted to cyber threats and take precautionary countermeasures before they materialize and spread,” he said. “Before CISA, corrective measures could be taken only after the cyber threat had done its damage. CISA allows each company to serve as an early warning system to the entire economy.”Who exactly would be determining if someone is a ‘threat’ is the meat of the sandwich, though. CISA is ripe for abuse, just as the Patriot Act has been.
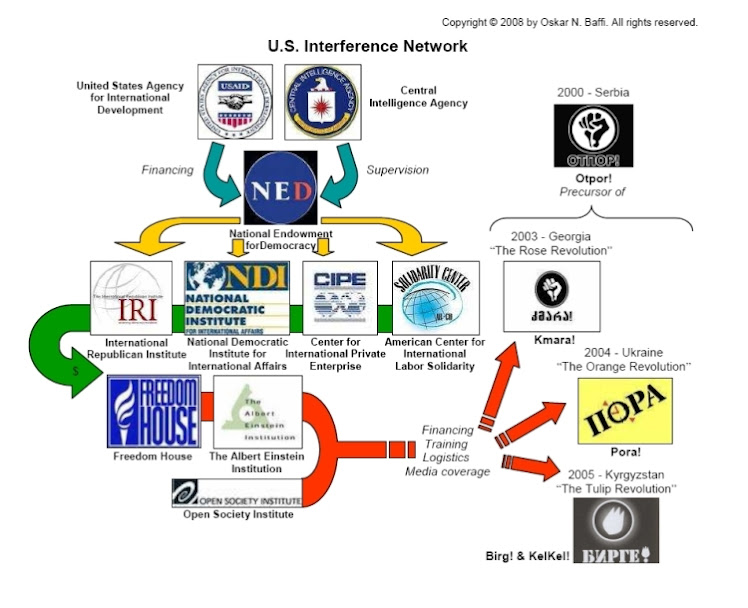
The stated purpose of the Patriot Act was to deter terrorist acts in the United States, but what do you do when the terrorists have already taken over your country? CISA simply expands the reach of a shadow government which has already been proven to reach beyond the boundaries of constitutional law.
More importantly, who specifically is CISA targeting? After multiple hackers have infiltrated computer systems at the White House, the State Department, the Pentagon, and the Office of Personnel Management, along with the Democratic National Committee, and numerous multinational banks run by the cabal, is the shadow government simply trying to create a stop-gap before their most elusive, yet damning information is made public?
CISA certainly will expand the reach of government surveillance on citizens as it has been conducted by the National Security Agency (NSA) before former NSA contractor Edward Snowden exposed it.
“I think this bill was meant to be a surveillance bill from the start,” said Justin Harvey, CSO of Fidelis Cybersecurity, adding that he is dubious that the stated intent of the bill – to use collective intelligence to warn of potential cyber attacks and possibly stop them before they occur – will result.
Under the guise of ‘sharing cyber threats’ CISA allows companies to wholesale-collect information that may not even be a threat – and then pass it along for government bodies to determine if it is, indeed a threat. If this sounds like circular logic – it is just the beginning of the odd verbiage within the bill. It’s justifications for entering every possible orifice for data-gathering are more confounded than an octopus in a straight jacket.
The government can already enter your personal property including your home, your body, your cell, and your computer, but now they will have a legal in-roads to declare you a cyber-threat, simply for sending an email. This begs the question – who is the real cyber-bully? CISA seems to be nothing more than a prevarication, covering the acts of an elite few who don’t want their secrets exposed.
Nathaniel Mauka is a researcher of the dark side of government and exopolitics, and a staff writer for Waking Times.
This article (Distracted by Election 2016, No-one Resisted the Deep State’s Patriot Act 2) was originally created and published by Waking Times and is published here under a Creative Commons license with attribution to Nathaniel Mauka andWakingTimes.com. It may be re-posted freely with proper attribution and author bio.
~~ Help Waking Times to raise the vibration by sharing this article with friends and family…