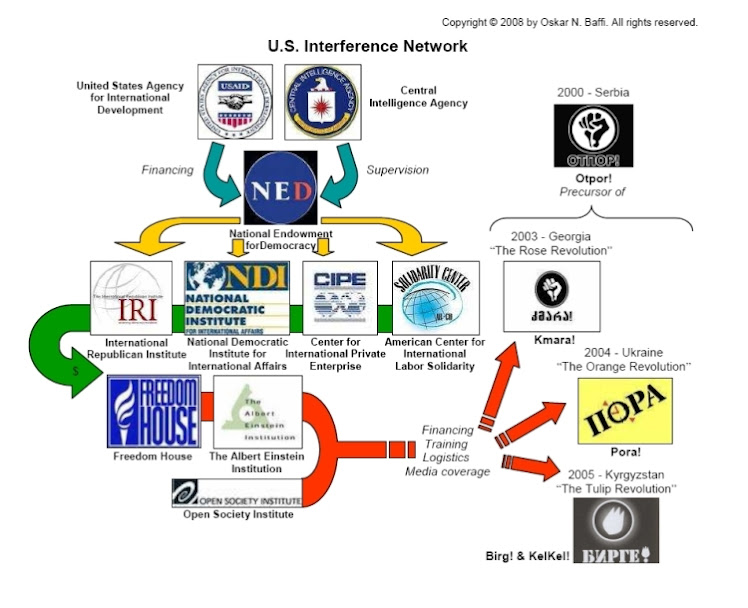
Only moments ago, WikiLeaks released what it claims to be the largest ever release of confidential documents on the CIA. This dump comes on the heels of a preview that the Free Thought Project reported on last month, in which WikiLeaks released documents showing the CIA’s role in interfering with French elections. This dump, however, is the apparent mother lode, which the transparency organization allegedly obtained from the CIA’s Center for Cyber Intelligence in Langley. It involves a massive cache of data ranging from the years 2013-2016.
Inside this data, according to WikiLeaks, are the tools the CIA has been using for years to wreak digital havoc on the world. According to the release:
Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.WikiLeaks notes that this is only the first part of a series they are calling “Year Zero,” which is comprised of 8,761 documents and files from an isolation high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virginia.
“Year Zero,” according to WikiLeaks, introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
This leak exposes the massive hacking powerhouse the CIA has become in the last decade — surpassing even that of the NSA.
Since 2001 the CIA has gained political and budgetary preeminence over the U.S. National Security Agency (NSA). The CIA found itself building not just its now infamous drone fleet, but a very different type of covert, globe-spanning force — its own substantial fleet of hackers. The agency’s hacking division freed it from having to disclose its often controversial operations to the NSA (its primary bureaucratic rival) in order to draw on the NSA’s hacking capacities.What is also notable about this leak is the fact that it reveals another Snowden-type whistleblower within the massive spying apparatus. This time, however, knowing how the US treats whistleblowers, the source has chosen to remain anonymous.
Cyber weapons pose a massive threat to the entire world’s infrastructure as they can be used by anyone from rival states, cyber mafias, and even teenage hackers.
According to Julian Assange, “There is an extreme proliferation risk in the development of cyber ‘weapons’. Comparisons can be drawn between the uncontrolled proliferation of such ‘weapons’, which results from the inability to contain them combined with their high market value, and the global arms trade. But the significance of ‘Year Zero’ goes well beyond the choice between cyberwar and cyberpeace. The disclosure is also exceptional from a political, legal and forensic perspective.”
Noting the severe implications of releasing these hacking tools publicly, WikiLeaks will avoid distributing the ‘armed’ version of the cyber weapons “until a consensus emerges on the technical and political nature of the CIA’s program and how such ‘weapons’ should analyzed, disarmed and published.”
To quantify the sheer size and scope of Vault 7, WikiLeaks notes that just part 1 “already eclipses the total number of pages published over the first three years of the Edward Snowden NSA leaks.”
One of the most ominous techniques profiled by WikiLeaks in Vault 7 is “Weeping Angel,” developed by the CIA’s Embedded Devices Branch (EDB) — a cyber weapon that infests smart TVs and transforms them into microphones.
This little device delivers turnkey Internet privacy and security (Ad)
As WikiLeaks reports, after infestation, Weeping Angel places the target TV in a ‘Fake-Off’ mode, so that the owner falsely believes the TV is off when it is on. In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server.Upon news of ‘Weeping Angel,’ Kim Dotcom chimed in, noting that it is not just TVs the CIA can control to spy on you.
BREAKING: CIA turns Smart TVs, iPhones, gaming consoles and many other consumer gadgets into open microphones. #Vault7— Kim Dotcom (@KimDotcom) March 7, 2017
Obama accused Russia of cyberattacks while his CIA turned all internet enabled consumer electronics in Russia into listening devices. Wow!— Kim Dotcom (@KimDotcom) March 7, 2017
The CIA’s Mobile Devices Branch (MDB) developed numerous attacks to remotely hack and control popular smart phones. Infected phones can be instructed to send the CIA the user’s geolocation, audio and text communications as well as covertly activate the phone’s camera and microphone.WikiLeaks put the world on notice with the news of the encrypted torrent file Vault 7 last night, and, at 8:06 am EST, they tweeted out the key to unlock it.
Despite iPhone’s minority share (14.5%) of the global smart phone market in 2016, a specialized unit in the CIA’s Mobile Development Branch produces malware to infest, control and exfiltrate data from iPhones and other Apple products running iOS, such as iPads. CIA’s arsenal includes numerous local and remote “zero days” developed by CIA or obtained from GCHQ, NSA, FBI or purchased from cyber arms contractors such as Baitshop. The disproportionate focus on iOS may be explained by the popularity of the iPhone among social, political, diplomatic and business elites.
A similar unit targets Google’s Android which is used to run the majority of the world’s smart phones (~85%) including Samsung, HTC and Sony. 1.15 billion Android powered phones were sold last year. “Year Zero” shows that as of 2016 the CIA had 24 “weaponized” Android “zero days” which it has developed itself and obtained from GCHQ, NSA and cyber arms contractors.
These techniques permit the CIA to bypass the encryption of WhatsApp, Signal, Telegram, Wiebo, Confide and Cloackman by hacking the “smart” phones that they run on and collecting audio and message traffic before encryption is applied.
The CIA also runs a very substantial effort to infect and control Microsoft Windows users with its malware. This includes multiple local and remote weaponized “zero days”, air gap jumping viruses such as “Hammer Drill” which infects software distributed on CD/DVDs, infectors for removable media such as USBs, systems to hide data in images or in covert disk areas ( “Brutal Kangaroo”) and to keep its malware infestations going.
Many of these infection efforts are pulled together by the CIA’s Automated Implant Branch (AIB), which has developed several attack systems for automated infestation and control of CIA malware, such as “Assassin” and “Medusa”.
Attacks against Internet infrastructure and webservers are developed by the CIA’s Network Devices Branch (NDB).
RELEASE: CIA Vault 7 Year Zero decryption passphrase:SplinterItIntoAThousandPiecesAndScatterItIntoTheWinds
— WikiLeaks (@wikileaks) March 7, 2017
NOTICE: As Mr. Assange’s Perscipe+Facebook video stream links are under attack his video press conference will be rescheduled.— WikiLeaks (@wikileaks) March 7, 2017
WikiLeaks published as soon as its verification and analysis were ready.Finally, WikiLeaks leaves the rest of the data mining up to the public.
In Febuary the Trump administration has issued an Executive Order calling for a “Cyberwar” review to be prepared within 30 days.
While the review increases the timeliness and relevance of the publication it did not play a role in setting the publication date.
WikiLeaks has intentionally not written up hundreds of impactful stories to encourage others to find them and so create expertise in the area for subsequent parts in the series. They’re there. Look. Those who demonstrate journalistic excellence may be considered for early access to future parts.The Free Thought Project is one of those outlets that will be bringing you our analysis of important information we find within these leaks. We will keep you updated as this, the largest leak in US history, unfolds.
Matt Agorist is the co-founder of TheFreeThoughtProject.com, where this article first appeared. He is an honorably discharged veteran of the USMC and former intelligence operator directly tasked by the NSA. This prior experience gives him unique insight into the world of government corruption and the American police state. Agorist has been an independent journalist for over a decade and has been featured on mainstream networks around the world. . and now on Steemit